Information Security directives that the RBI has laid down for NBFCs have very well defined, practical sections for both Information Security as well as Cybersecurity. To quote the ‘Master Direction – Information Technology Framework for the NBFC Sector,’ the following are the basic tenets that uphold the importance of secure access to information and proper authorisation.
Confidentiality – Ensuring access to sensitive data to authorized users only. Integrity – Ensuring the accuracy and reliability of information by ensuring that there is no modification without authorisation.
Availability – Ensuring that uninterrupted data is available to users when it is needed.
Authenticity – For Information Security, it is necessary to ensure that the data, transactions, communications, or documents (electronic or physical) are genuine.” Further, these tenets and their stress on enabling the right access with the right information hit home with ‘Identity Security.’ Compact Identity can singlehandedly strengthen your organization’s Identity Security and take NBFCs from 0 to compliant in as less as 90 days.
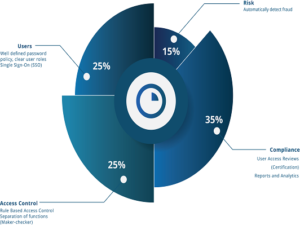
Security and regulatory compliance are not as tricky as they are believed to be. More so, when your expectations are tempered with reality. As long as you have an agile and equally practical partner who offers an all-in-one solution, compliance and security will be simpler than you ever imagined them to be! Let us understand the core pillars of Identity Security and how the right solution will be able to fortify walls around critical data. When these are well managed, simple steps will take you to full regulatory compliance as well as build adequate IT security.
- Access Management Start with password management
Automated password management delivers over 700% ROI despite its simplicity. Single Sign-On dramatically improves productivity and offers over 2,700% ROI. While the most significant challenge here could often be of building the right connectors to the apps you want access to, partnering with a business solution provider who understands market needs can dramatically resolve that challenge. And, Ilantus is the fastest and lowest cost connector company in the market! To be able to deliver Role-Based Access Control specified by the RBI, NBFCs must simplify managing roles and ensure that they are well defined and possibly integrated with Active Directory. Further, supporting data import from various sources, including automatic roles based on user parameters, is something that partnering with Compact Identity can deliver flawlessly.
- Identity Lifecycle Management
Managing the ‘Identity’ from onboarding to promotions/movements until its eventual termination is often an IT nightmare. New hires spend their initial days awaiting accesses, and after an employee leaves accounts are not terminated in time. Poor management of Identities causes significant productivity loss in addition to putting the organization’s security posture in jeopardy. Compact Identity automates this journey of movers-joiners-leavers with ease, ensuring that users do not have unwanted accesses; at the same time granting new accesses automatically. In addition, Compact Identity will be able to automate the cycle such that it takes IT minutes, not hours to provision or deprovision users.
- Identity Governance
Identity Security works best with an effective level of Governance. Audits and reviews are critical to ensuring that identities and accesses are in conformance with policy. Compact Identity will be able to deliver an integrated access review system that supports multiple level approvals and automatic removal of accesses denied during reviews. One of the most critical elements of Governance and compliance with RBI directives can be achieved through Compact Identity’s integrated capability. Identity Governance is crucial to ensuring that compliance is an actual operational priority for your organization. Effective periodic certification and re-certification of accesses ensures continuous monitoring of accesses with minimal disruption to business as usual.
- Privileged Access Management (PAM)
Every organization relies on ‘administrators’ for management of IT solutions. Both internal IT staff and external IT consultants have access to critical IT resources and business data – generally at the ‘root’ level. Such accesses are extremely vulnerable to breaches and are most likely to be the targets of threat actors. When you plan your compliance programme with Compact Identity, you are assured of a world-class Privileged Access Management (PAM) experience with state-of-the-art capabilities to manage these accesses.
- Integrated Risk Engine
The right Risk Engine within an Identity Security solution augments security with automated controls and system alerts. In addition to taking full advantage of external threat information, Compact Identity digests signals from real-time user access and historical data (such as the last time a user’s accesses were certified) to deliver continuous risk review. The Compact Identity Risk Engine complements the other four pillars of Identity Security to deliver essential intelligent automation to support your manual efforts.
Backed by over 19 years of IAM expertise, Ilantus is a global provider of cloud Identity and Access Management solutions. We strive to make worldclass, economical, and intelligent IAM accessible to all organizations.
Ilantus was recently named an Innovation Leader by KuppingerCole, the most acknowledged IAM-only analyst. With over 500 global implementations under our belt, one of which is a bank in India we brought to full regulatory compliance in less than 90 days!
With our top Global and Indian technology partners, you can be assured of a successful rollout and compliance with all relevant RBI guidelines – all at the lowest TCO in the industry!
For further details on how you could leverage Compact Identity for your organization, reach out to us across the following: www.ilantus.com Phone: +91 636.161.4717 +91 808.843.2938 Email: inquiry@ilantus.com
Elets The Banking and Finance Post Magazine has carved out a niche for itself in the crowded market with exclusive & unique content. Get in-depth insights on trend-setting innovations & transformation in the BFSI sector. Best offers for Print + Digital issues! Subscribe here➔ www.eletsonline.com/subscription/