 Sysdig Inc., the secure DevOps provider, unveiled Sysdig Secure 3.0, industry’s first tool to offer enterprises with threat prevention at runtime via Kubernetes-native Pod Security Policies (PSP).
Sysdig Inc., the secure DevOps provider, unveiled Sysdig Secure 3.0, industry’s first tool to offer enterprises with threat prevention at runtime via Kubernetes-native Pod Security Policies (PSP).
PSPs are the controls in Kubernetes that signify the security conditions pods must observe in a bid to run. Sysdig Secure 3.0 also involves the first incident response and audit tool for Kubernetes, offering enterprises the ability to reconstruct historical system activity.
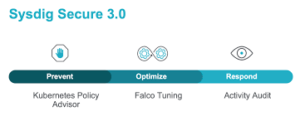
Enabling these capabilities are three new features: Kubernetes Policy Advisor, Falco Tuning, and Activity Audit. This release emphasises on securing Kubernetes environments throughout the entire lifespan, analysing vulnerabilities and misconfigurations in the build phase, stopping threats without effecting performance during the run phase, and enabling an incident response, forensics, and audit.
Kubernetes is the de facto operating system of cloud; however, as organisations shift workloads into production, security and visibility are the biggest hindrances. Traditional tools and processes do not offer visibility with context for Kubernetes environments. Moreover, traditional roles are ging for a paradigm shift as security is embedded across the build, run, and respond phases of the application lifecycle. In a bid to ensure secure and compliant containerised applications, enterprises are shifting away from siloed functions and introducing a secure DevOps workflow.
“When operating containers, the only way to manage risk without slowing down the CI/CD pipeline is to embed security and compliance across the entire Kubernetes lifecycle,” said Suresh Vasudevan, Sysdig Chief Executive Officer. “Kubernetes has the ability to be more secure than VMs, but there are certain security and visibility elements enterprises must address, which includes adopting Kubernetes-native tools and a secure DevOps approach.”
Elets The Banking and Finance Post Magazine has carved out a niche for itself in the crowded market with exclusive & unique content. Get in-depth insights on trend-setting innovations & transformation in the BFSI sector. Best offers for Print + Digital issues! Subscribe here➔ www.eletsonline.com/subscription/




















